
Security and Compliance at Ariadne (and What it Means for your Data Security and Compliance Needs) Part – 1
Stephanie Pasas Farmer, PhD
President and Founder at Ariadne Software
When a new software tool is launched in the pharmaceutical industry, it invites a lot of excitement and skepticism, which may grow further if the software uses a form of artificial intelligence. Given the highly regulated nature of the industry and the criticality and sensitivity of the data, the early adopters willing to learn about it or try it, almost always ask about security and compliance next.
Ariadne Software® developed its primary product, Red Thread®, to fill the void of an automated system to audit bioanalytical data for pharmacokinetic and immunogenicity data as well as provide statistical analysis for immunogenicity/anti-drug antibody (ADA) data. The Software as a Service (SaaS) offering allows our clients to focus on bioanalysis while leaving the needs of physical, environmental and compute infrastructure to us. All they need to do is to the upload their data so the cloud-based software can audit it and highlight trends of importance within their pharmacokinetic and/or immunogenicity data. Red Thread essentially looks through the data provided and generates “flags” that help instruct plans for further scientific analysis or a need for re-analysis. Our clients can also upload their ADA data for cut point determination and sensitivity analysis for a robust and objective analysis that brings a consistent statistical approach to each analysis. These offerings are extremely valuable to our customers, so as a next step, they want to ensure that our software tool is secure and compliant to best industry practices.
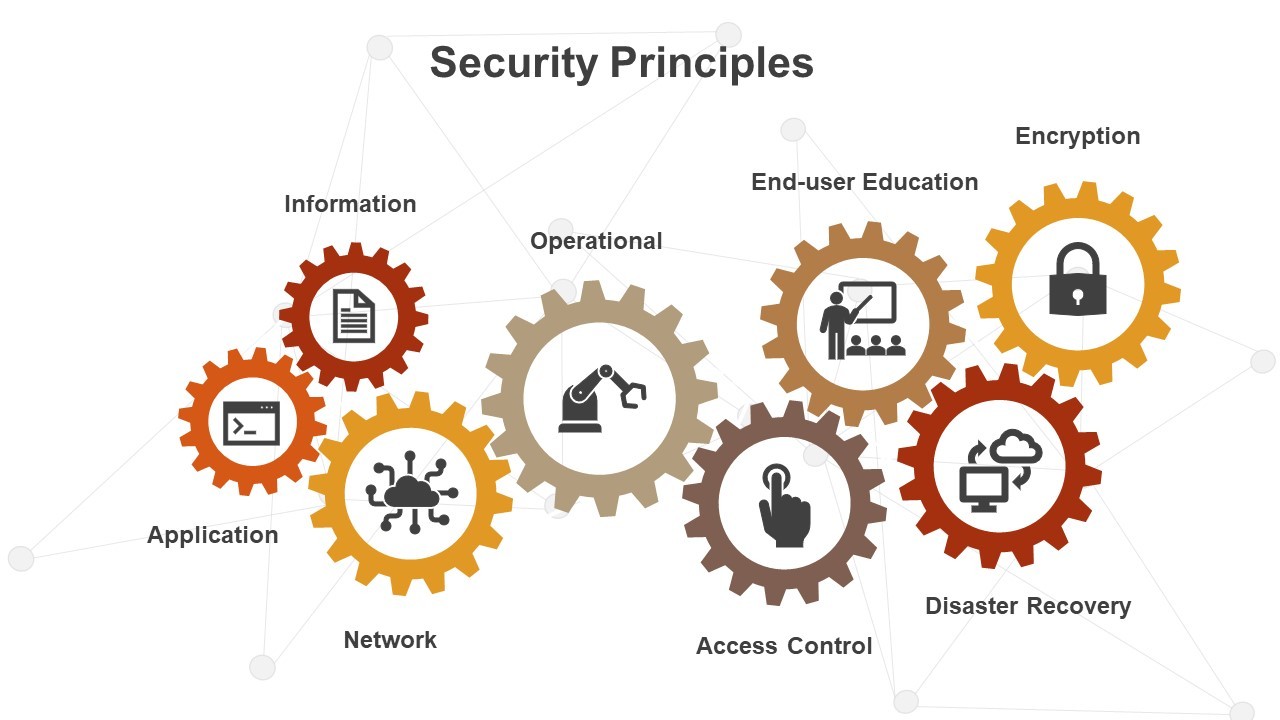
What is Security in the World of Pharmaceutical SaaS?
We often get asked: Are we saving any proprietary/sensitive data? How long does the software “keep” the information? Does the software provide an audit trail? Are we encrypting the data as it is uploaded? How do we manage and address security incidents and disaster recovery? Do we comply with 21 CFR Part 11 guidelines? Do we have any security certifications?
Consequently, as developers of the software, it is very important for us to consider the answers to these questions, even before they are asked. Not only does it build trust within our customers, but it also shows them that we were thinking about these concerns from the beginning of our process. One of the first things we decided was to follow a security and compliance framework. In fact, we ended up opting for three: FDA’s 21 CFR Part 11, International Organization for Standardization’s (ISO) ISO 27001 and Service Organization Control’s (SOC) SOC 2 frameworks.
A Brief Introduction to Some Security Frameworks
While all three frameworks are geared toward providing guidance for information security management systems (ISMS), the 21 CFR Part 11 governs the handling of electronic records and signatures, whereas the ISO 27001 and SOC 2 frameworks dictate ISMS guidelines for an organization to secure all their information assets – systems, people, and processes. Also, while ISO 27001 and SOC 2 can be certified, FDA does not certify 21 CFR Part 11 compliance. Between ISO 27001 and SOC 2, ISO 27001 is more focused on the successful establishment of and compliance to policies, processes, and the people, whereas SOC 2 goes into process details and looks at evidence for the selected observation period and is more rigorous towards implementation of the systems, people, and processes that are a part of the ISMS.
Through 21 CFR Part 11, the FDA has offered guidance for organizations to follow if they are working with electronic records and electronic signatures. An electronic record is any information that is either created, processed, stored, maintained, and/or transmitted online. An electronic signature is a unique name and a date and time stamp associated with an electronic activity. This could be a sign in into an application, or name and date for approval of an electronic record, or an audit trail for a software. Although not certifiable, FDA expects all organizations to follow the guidelines outlined in 21 CFR Part 11 for their electronic records and signatures.
Then we have ISO 27001 and SOC 2 that focus on confidentiality, integrity, and availability of information. Although, SOC 2 goes a step further and also focuses on data privacy and overall security, which is briefly touched upon in ISO 27001. ISO 27001 verifies operational maturity of ongoing information security of an organization whereas SOC 2 ensures that information system is implemented in such a way that it can protect customer data. Certification/Attestation is issued by an accredited certification body only when an organization can demonstrate competence of maintaining information system as per controls defined by security framework. There are also some other frameworks, such as GDPR, which deals with privacy of information and which we also comply with.
Apart from offering the client the security of 21 CFR Part 11 along with ISO 27001 and SOC 2 Type I framework certifications, the internal decision behind utilizing these meant that we would be following a stricter checklist in our processes with universal expectations. It meant that we continuously strive to be more sincere in our pursuit of the development process for all stakeholders involved, that all processes could be more easily audited, and that there would be a clear sense of accountability for each part. With the combination of these multiple framework certifications in place, we established clear guidelines for our use of cloud platforms, general security, and the handling of proprietary client data and Ariadne intellectual property alike.
Security Measures at Ariadne
In compliance with ISO 27001 and SOC 2 Type II, Ariadne follows policies and procedures pertaining to software development, access management, handling of client or Ariadne information, managing and communicating security incidents, acceptable employee conduct, risk management, vendor management, and more. Apart from following ISO 27001 and SOC 2 trust principles, Ariadne is committed to work with its clients and address their security concerns. As an additional security measure, Ariadne deletes the client data right after processing, and only maintains the output report (with little to no proprietary data) within the software and the audit log. We, thereby, do not hold onto client’s proprietary data (except analyte name in most cases). Any data, including audit trail, is saved for 10 years. We can delete client’s data (audit or statistical analysis report, and data files, if shared with us separately) upon client request, but as required per regulatory guidelines, we cannot delete the audit trail. We also offer encryption for client data, while in transit, i.e. during the uploading of the data file. Additionally, by using Amazon Web Services (AWS), which not only provides cloud infrastructure to host the software, but also offers audit trail, user management and various security applications, we are able to offer a highly secure SaaS offering. To ensure security and compliance, AWS itself undergoes ISO 27001, SOC 2 Type II and several other certifications each year.
It is with this process that we are able to offer such security to our customers from the very beginning of the relationship. More importantly, this allows us to answer a number of questions long before they are asked. Additionally, as a result of this commitment, Ariadne received our ISO 27001 in January 2022 and our SOC 2 Type I certification in July 2022. I would also like to emphasize that this is not a one-time process, and we strive to keep up with the certification/re-certification process on an annual basis.
Building upon the compliance at Ariadne, we will discuss validation as another key aspect of offering a compliant software in Part 2 of the blog post.
Meanwhile, I encourage to provide your comments and or ask any questions with regards to security and compliance by responding to this post. To learn more about Red Thread, please visit our website or contact us at info@ariadnesolutions.com.
